Passwords were never a security tool so much as a story we told ourselves about control. You invent a secret, you keep it in your head, you prove you are you by producing it on demand. That story worked just long enough for the internet to become essential, and then it collapsed under the weight of scale, repetition, phishing, leaks, and the simple reality that human memory is not an authentication system. What replaced it was not a better secret. It was a different idea entirely: stop trusting what a person knows, start trusting what a device can prove.
Passkeys look like convenience. They are marketed as faster logins, fewer resets, less friction. That is true, and it is also camouflage. The larger change is architectural. Passkeys move authentication away from shared secrets and toward cryptographic possession, with public keys stored by services and private keys kept inside hardware-backed vaults on devices. The secret stops being a phrase that can be copied. It becomes a capability that can be used without being revealed.
In that shift, security improves, yes. Something else shifts too: leverage. Who owns the keys to identity, who can recover access, who can audit risk, and who gets blamed when people are locked out. Passkeys do not merely eliminate passwords. They redraw the map of trust on the internet.
The quiet failure mode that made passwords inevitable
Passwords did not become dominant because they were good. They became dominant because they were cheap. A password is storage and comparison. It asks nothing of hardware, little of bandwidth, and almost nothing of user education beyond “do not forget.” The cost was externalized to everyone else: support teams handling resets, users living with constant low-level anxiety, and security engineers building a maze of compensating controls around a fragile core.
That fragility took predictable shapes. Humans reuse credentials because they must. Attackers harvest those credentials and try them elsewhere because it works. Phishing thrives because the “proof” is easily transferable. A password can be entered anywhere, into anything, under any story. The infrastructure of the modern scam economy is built on that portability. If the credential is just a string, the only barrier is persuasion.
Then came the industrialization of leaks. The internet’s memory is long, and breaches do not expire. A password can be strong and still become weak the moment it leaves the user’s head and enters a database, because databases can be stolen. Even when stored as hashes, the economics of cracking can still favor attackers for large datasets, and the downstream effect is the same: recycled credentials become a weapon.
You can patch this with second factors, but second factors have their own compromises. Text messages are vulnerable to interception and number porting. Push prompts can be abused through fatigue and deception. One-time codes can be phished and replayed in real time. Many “two-factor” schemes still revolve around a password at the center, which means the house is still built on a door that can be tricked open if the occupant is persuaded.
Passkeys are the attempt to stop persuading humans to be better at something humans are structurally bad at.
What passkeys actually are when you strip away the marketing
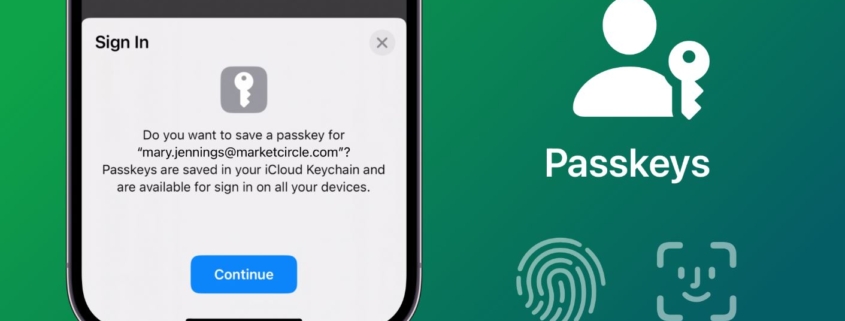
A passkey is a public key credential tied to a specific account and a specific service. When you sign in, the service sends a challenge, your device signs it using a private key, and the service verifies the signature using the public key it already has. The private key never leaves the device in any readable form. In many implementations, it is stored in a secure hardware enclave or module that is designed to resist extraction.
This architecture changes the nature of theft. With passwords, a phishing page can steal the credential directly. With passkeys, there is nothing meaningful to steal from the user, because the user is not transmitting a reusable secret. The user is authorizing a signature operation, and that signature is valid only for that moment and that service.
There is also a built-in lock against the most common form of impersonation. Passkeys are bound to the origin of the website or app. The cryptographic exchange is designed so that a credential created for one site cannot be used for another, even if the interface looks identical. This does not end social engineering, but it turns many of today’s scams into dead ends.
Seen clearly, passkeys are less like a better password and more like a distributed hardware token system that became mainstream by hiding inside devices people already carry.
The device becomes a credential, and that changes the psychology of access
Passwords live in the mind, at least in theory. Devices live in the world. The moment authentication depends on a device, identity starts to feel physical again. You “have” access in the same way you have a wallet or a house key. Lose the object and you lose the ability, even if your knowledge remains intact.
That shift has emotional consequences. For many people, losing a password is annoying. Losing a phone can be terrifying. Passkeys attach account access to something that can be dropped in water, stolen on a train, or locked behind a forgotten screen code. The technology is resilient in cryptographic terms, but it changes what people fear.
This is one reason passkey adoption is not only a security project. It is a user trust project. If people believe passkeys will lock them out more often than passwords did, they will resist, even if passkeys reduce hacking risk. Humans do not experience security as an abstract reduction of probability. They experience it as whether their life stays intact during a crisis.
That crisis is usually not a sophisticated attacker. It is a broken device at the wrong time.
Recovery is the real battlefield
The hardest part of any authentication change is not logging in on a good day. It is recovering on a bad day. Password systems have a brutal simplicity here: you can reset a password if you can prove something else, often an email address, a phone number, or a set of security questions that are not actually secure. This is messy, but it is familiar.
Passkeys make recovery both better and more dangerous.
It gets better because recovery can be engineered around device ecosystems that sync credentials across trusted devices, allowing you to sign in on a new phone using a tablet or laptop you already own. It can also be built around multiple passkeys per account, so you are not dependent on a single object. In principle, passkeys can reduce the frequency of desperate account recovery requests because authentication becomes easier and more consistent.
It gets more dangerous because recovery becomes a single point of social engineering. If a service can restore access to someone who has lost their passkey, that restoration process becomes the new password reset, and attackers will target it relentlessly. The more seamless the recovery, the more attractive it becomes as an attack surface.
This is the hidden paradox. Passkeys eliminate many forms of credential theft, which increases pressure on customer support and recovery channels, because those channels become the easiest remaining route. If an attacker cannot steal your secret, they will attempt to become you in the service’s eyes.
A passkey world, if designed poorly, simply moves fraud from phishing sites to help desks.
Biometrics are not the credential, and misunderstanding that creates panic
Many people think passkeys mean “your face is your password.” This is one of the most persistent misconceptions, and it matters because it triggers understandable fears about privacy and surveillance.
Biometrics in passkey systems typically function as a local unlock method, not as the credential itself. The face scan or fingerprint is used to authorize the device to use the private key. The biometric data, in well-designed systems, stays on the device and is not transmitted to the service. The service sees only a cryptographic proof, not your fingerprint.
This distinction is crucial because it reframes what is at stake. The risk is not that a website obtains your biometric. The risk is that someone obtains your device unlock, or coerces you into unlocking it, or exploits weaknesses in device security.
That risk is real. It is simply different. It also interacts with social reality. A fingerprint can be compelled more easily than a memorized secret. A face can be used while you are asleep. People have different threat models based on their lives. A journalist, an abuse survivor, a political dissident, or a person in a coercive relationship may view biometric unlock very differently than someone who worries primarily about hackers.
Passkeys do not erase these differences. They make them more salient, because authentication becomes embodied.
Portability is the promise, lock-in is the fear
Passkeys are built on standards, which suggests interoperability. Yet the lived experience of interoperability depends on how devices and services implement those standards. For many users, passkeys will be encountered through operating systems and password managers that sync credentials in a way that feels like an ecosystem feature.
That creates a tension. The more smoothly passkeys sync, the more people will rely on a particular platform’s cloud. Reliance can feel like safety, until it feels like captivity. Changing phones becomes changing identity infrastructure. Switching between ecosystems can feel like emigrating.
This is not a purely technical issue. It is a market issue. If passkeys become the default login method for major services, then the entities that control the most convenient passkey storage and syncing become gatekeepers of everyday access. They will not need to be malicious to create dependence. Convenience is enough.
The ideal future is one where passkeys can be exported, managed, and moved across tools without drama, with clear user consent and predictable recovery. The cynical future is one where portability exists in theory but feels punishing in practice, a maze of partial transfers and awkward prompts that quietly encourage people to stay put.
People tolerate lock-in when it feels like stability. They resent it when it feels like power being exercised over them.
Enterprises are not adopting passkeys for the same reason consumers are
For an individual, passkeys are about ease and safety. For a company, passkeys are about reducing cost and reducing embarrassment.
Password resets are expensive. Help desk calls are expensive. Breaches caused by credential stuffing are expensive, not only in money but in reputation. Companies also operate under compliance regimes that demand demonstrable controls. Passkeys promise to reduce a whole category of common attacks, and they promise to simplify employee access in ways that can be audited.
Yet enterprises also face a different set of fears. Device loss is common. Employee turnover is constant. Shared machines still exist in many workplaces. Contractors appear and disappear. A password can be changed instantly when someone leaves. A passkey tied to a device requires clean offboarding processes, device management policies, and a plan for credential revocation that does not depend on someone returning hardware politely.
This is where passkeys reveal their structural nature. They work best when identity, devices, and policy live in the same coherent system. Organizations with mature device management will thrive. Organizations with chaotic hardware practices will experience passkeys as another layer of complexity.
In a sense, passkeys reward institutional competence.
Attackers do not disappear, they migrate
It is tempting to treat passkeys as the end of the story, a final fix. Security does not work that way. When one path closes, pressure shifts elsewhere.
Credential stuffing becomes less effective where passkeys replace passwords. Phishing becomes harder where origins are bound and secrets are not transmitted. That does not end fraud. It redirects fraud into channels that remain human.
Expect more attempts at account recovery manipulation. Expect more malware designed to hijack sessions rather than steal passwords. Expect more attacks aimed at devices and their unlock methods. Expect more focus on stealing the cookies and tokens that represent authenticated sessions, because if you cannot become someone at login, you try to become them after login.
This is not pessimism. It is pattern recognition. The main victory of passkeys is that they raise the cost of casual, scalable credential theft. They force attackers to become more targeted, more invasive, or more dependent on social manipulation. That may reduce overall harm, but it will not eliminate it, and it may change who is harmed.
The most vulnerable people often face the most personal attacks, not the most industrial ones. Passkeys help against the industrial scale. The personal scale remains.
The UX problem is not prompts, it is trust rituals
A login flow is a ritual. It teaches people what to expect and what to fear. Password prompts teach people to type secrets. Two-factor prompts teach people to approve interruptions. Passkeys teach people to trust their device to speak for them.
For this to work culturally, the ritual has to feel stable. People need to see the same kinds of prompts in the same contexts. They need to understand what a legitimate system request looks like and what a scam looks like. They need to learn, quickly, that a passkey prompt is not asking for information, it is asking for consent.
This is why inconsistent design across apps and websites is not a minor inconvenience. It is a security flaw. If legitimate prompts vary wildly, users become accustomed to ambiguity. Ambiguity is where scams breed.
Passkeys are often described as frictionless. In reality, they replace one kind of friction with another. Instead of remembering, you must verify. Instead of typing, you must decide. That decision, repeated daily, becomes habit. Habit becomes safety when it is consistent and comprehensible.
A passkey world will be won or lost through small choices in interface design, not just through cryptography.
Shared devices expose a social edge case we pretend does not exist
Many authentication designs assume a personal device with a single owner. Many lives do not fit that model.
Families share tablets. Partners share laptops. Households share streaming accounts. Workplaces share terminals. People in precarious situations may borrow devices. In these contexts, passkeys can become either safer or riskier depending on how accounts and profiles are separated.
If passkeys are tied to a device profile and protected by a distinct unlock, they can be safer than passwords written on sticky notes. If passkeys are available to anyone who can unlock the device, they can create new domestic risks. When access becomes “who can unlock the phone,” social dynamics matter more than they did under a password system, because the credential is no longer a memorized secret that can be withheld.
This is one reason the passkey shift is not merely technical. It touches relationships. It touches coercion. It touches how people share and guard access in intimate spaces.
A technology that assumes clean ownership can become dangerous in messy human reality.
The deeper technical shift is that authentication becomes asymmetric by default
Passwords are symmetric. The same secret is used to verify identity. Symmetry is simple and also brittle. If the secret leaks, everything collapses.
Passkeys are asymmetric. A public key can be shared safely. A private key stays private. This is a long-standing principle in cryptography, but passkeys bring it into daily life for ordinary users at scale.
Asymmetry changes how services store identity. A breach of a passkey database yields public keys, which are not usable for impersonation in the same way stolen password hashes or plaintext credentials are. That is a major security improvement, and it also shifts legal and reputational risk. A service that stores fewer secrets becomes a smaller target. It also becomes easier to argue that a breach was less harmful, because the leaked material is less directly weaponizable.
This could change the economics of security investment. If passkeys reduce the catastrophic downside of database theft, some companies may become less motivated to invest in other controls, assuming the worst-case scenario is now contained. That assumption would be dangerous, because attackers will adapt, and because data beyond credentials still matters. Yet it illustrates how architecture shapes incentives.
Security is rarely about absolute protection. It is about where the weakest link sits, and who pays when it breaks.
Identity is slowly becoming a platform layer
Once passkeys spread, authentication begins to look less like an app feature and more like an operating layer shared across experiences. Your device becomes the mediator between you and services. The boundary between identity and platform blurs.
This has practical benefits. People can log in across devices more easily. Developers can rely on standardized flows. Services can reduce password infrastructure. Users can stop playing the memory game.
It also introduces strategic questions. If identity becomes a layer controlled by a few device ecosystems and credential managers, those systems gain a form of quiet sovereignty. They can shape defaults. They can influence which services feel trustworthy. They can define how recovery works. They can decide how portable identity really is.
When identity becomes a layer, it becomes a site of competition and regulation, because the ability to authenticate is the ability to participate. Losing access is not merely an inconvenience. It can mean losing your messages, your photos, your finances, your work tools, your social presence. Passkeys heighten this because they tie authentication more closely to device possession and ecosystem trust.
We tend to talk about identity as personal. At scale, identity is infrastructure.
What a passkey future does to culture, not just security
Passwords trained people to normalize mild distress. The constant fear of forgetting, the irritation of resets, the embarrassment of being locked out, the ritual of creating new variations of the same secret, all of it became background noise. People accepted that digital life required small humiliations.
Passkeys could remove some of that friction. That is a gift. It could also remove a certain kind of conscious engagement with identity. When you do not type a credential, you may stop feeling that you are actively proving yourself. You may start feeling that your device is you.
That seems harmless until you consider what happens when devices are lost, stolen, seized, or compromised. The psychological fusion of self and device can make digital vulnerability feel more existential. If your phone becomes the key to your life, your relationship to it changes. You guard it more. You fear its failure more. You may hesitate to let it out of your sight in ways that alter social behavior.
A society that ties identity to devices may become more cautious, more dependent, and more stratified between those who can afford reliable hardware and those who cannot.
The security story and the social story will not be separable.
The most important design choice is whether we treat lockout as inevitable or intolerable
In a passkey world, the most humane systems will be the ones that assume people will lose devices and will still deserve dignity. That means designing recovery that is strong enough to resist manipulation and gentle enough to rescue legitimate users without making them feel criminal.
It means encouraging multiple authenticators without turning setup into a chore. It means making revocation clear when a device is stolen. It means offering paths that do not depend solely on a phone number or an email account that could itself be compromised. It means acknowledging that some people need higher security and some need higher resilience, and that one size will not fit all.
If services treat lockout as an acceptable price for security, passkeys will become a niche success and a mainstream resentment. If services treat lockout as a crisis worth preventing, passkeys could become one of the rare internet changes that improves both safety and daily life.
This is the hinge. Cryptography can solve impersonation at login. It cannot solve the human catastrophe of losing access to your own existence online.
And once you notice that, you start to see passkeys not as the end of passwords, but as the start of a harder question, whether we want identity to be something you can misplace.